Access to the service providers’ servers and defacing hundreds of websites is not a major cyber event of the week.
The first lesson
During the 2008 Russian-Georgian War, cyber attacks against the Georgian government and media websites were carried out in parallel with conventional hostilities. Georgia was completely unprepared. The cyber attacks were part of an information warfare campaign aimed at suppressing the spread of information from Georgia.
The Ministry of Foreign Affairs website was among the targets. Therefore the Ministry of Foreign Affairs was forced to use alternate channels and posted the news on the Blogspot platform. Georgian government and media outlets have been able to continue operating in cyberspace only with external support. External assistance was required to investigate the incidents and to identify and eliminate the weaknesses that made the attack possible.
It should be noted that at that time Russia did not need to use any sophisticated mechanisms for cyber attack. Successful attacks on the Georgian websites was easily possible because of a low level security, numerous unresolved technical weaknesses, and the lack of basic cyber security expertise…
For more on this topic, see the New York Times article.
Failed law
Following the cyber collapse of 2008, a computer-based incident response team was set up, tasked with recording and investigating public and private incidents. Work on information security law has begun. The Information Security Bill was adopted in 2012 (see law at matsne.gov.ge).
The law established a minimum standard of information security, which was an adapted version of ISO 27001 in Georgian. It identified 39 critical information infrastructure (all of them from public sector) that were tasked with implementing the law within 3 years.
By 2018, out of 39 entities, several (up to ten) state organizations met the requirements of the law. It can be said that the law has failed. Over time, several causes of failure have been identified.
Reasons for the failure of the law
If you read the ISO 27001 standard (or any other standard that applies to the general management systems, information security management or quality management systems), the very first paragraph states that “management support” is needed to implement the information security management system. This support in the organization is expressed by allocating relevant resources and prioritizing the information security. Exactly the same thing is needed countrywide.
Alas, cyber security has never been one of the government’s priorities. Nor did the law provide any penalties for non-compliance. Finally, the requirements set out in the law prepared by the Ministry of Justice were partially implemented by the LEPLs of the Ministry of Justice and the National Bank (the National Bank also passed ISO 27001 international certification).
We came to the second problem – the LEPL Data Exchange Agency of the Ministry of Justice was responsible for the implementation and coordination of the law. Obviously, the Ministry of Justice’s LEPL found it difficult for other ministries and their LEPLs to make them to comply with the requirements, especially since no punitive leverage was provided by the law.
Speaking about the failure of the law, the lack of human resources has also been mentioned. The US and UK also lack human resources in cyber security, so this problem was expected in Georgia. But in here, cyber security was not among the government’s priorities. As a result, those 39 government entities also did not prioritize the information security, which in all diminished the growth of cyber security.
Speaking about the shortcomings of the law, they also mentioned that the law did not apply to the private sector, such as the banks or the energy sector. However, even where it was spread has failed drastically and did not have an effect that was estimated.
The new draft law
Some time ago came up the idea of the need of revision and the information security bill has been drafted. This new bill is set to be voted on in parliament in November and if passed, will come into force on January 1, 2020. See the draft law on the Parliament’s website.
The law gives cause for concern for several aspects. It neither takes into account past mistakes, nor the experience of other countries, poses a risk of total control, and the proposed modifications are unlikely to improve the cyber security environment in the country.
The law defines three categories of critical information infrastructure: 1. Public sector; 2. Telecommunications Sector; 3. Private Sector;
A new actor is coming in: Operational-Technical Agency (OTA), which will be the LEPL of the State Security Service. OTA will coordinate the first and second category organizations, while the data exchange agency will coordinate the private sector (third category).
What OTA is entitled to? The risk of total control.
In state organizations (first category entities) the OTA will have the right to request the implementation of its own network sensor to detect incidents. The network sensor is expected to pass through the full network traffic (until now the sensor network was managed by the Data Exchange Agency).
- Upon request, Category 1 and Category 2 entities shall be given access to the information asset, information system and / or information infrastructure subject if such access is required to respond to an ongoing or occurring computer incident. According to the record, it will be possible for OTA to access entities’ information systems virtually without interruption. The LEPL of SSSG (State Security Service of Georgia) has the opportunity to gain access to the information systems, databases, firewalls, etc. of state and telecommunications organizations. We will also clarify that the state organizations ay mean any state ministry, parliament, etc…
- With the consent of the Critical Information System Entity of the second or third category, the Operational-Technical Agency, the Data Exchange Agency, or a person or organization selected by the Critical Information System Entity from its authorized auditors shall conduct an information security audit. After conducting the audit, a conclusion is drawn up with the requirements, which are mandatory to comply. One copy of the audit report (conducted by the Data Exchange Agency or its authorized person) shall be sent to the Operational-Technical Agency. In any case, audit reports on the weaknesses of the second and third category of subjects are sent to the OTA, which will be informed about all critical private (e.g. banks) and telecommunication organizations weaknesses.
- In addition, OTA is entitled to carry out planned or unplanned audits in the first category of entities, including: internal network, external network access point, network configuration, software and / or hardware used for network operation as well as its security, software and / or hardware connected to the network used for receiving, processing, storing and transmitting data, formalized or non-formalized rules and procedures for incorporating software and / or hardware into the network. In fact, even without the incident, OTA will be able to request access to the subsystems.
Three CERTs and two regulators
A second state-owned CERT in operational-technical agency is being formed. It is unclear why another public CERT should be created when no one has complained about Data Exchange Agency’s CERT work. They have implemented several successful projects.
Why are competencies divided when human resources are already so scarce? Another question is how these two groups will be able to coordinate. Or why complicate matters with the addition of a new structure and the need for coordination? It should also be noted that the Ministry of Defense had another state CERT (within the Bureau of Cyber Security) and it was not subject to change.
According to the draft law, the OTA and the Data Exchange Agency should jointly publish the information security standard. It is unclear what the division of competencies between the Data Exchange Agency and OTA serves. Why should 2 organizations publish 1 standard? In which country is there such a precedent?
National Bank Regulation for Banks
Another issue is the entities of the third category, which are expected to include banks as well. The National Bank has already released a cyber security framework based on the American NIST cyber security framework. In fact, both the law and this framework require the implementation of an information security management system. It is incomprehensible why two regulators need the same topic with the same requirements? Was the National Bank not involved in drafting the law? Why not coordinate with the National Bank when drafting the law? If the National Bank was involved in drafting the law and still remained the subject of 2 regulators on the same issue?
The practice of European countries
In the western world, there is no precedent of establishing cyber security standards in the country and increasing the level of cyber security was part of a state security or intelligence services mission. In Estonia, for example, the cyber security sector is run by an organization under the Ministry of Economy. See Estonian cyber security law.
State Audit Office out of the game
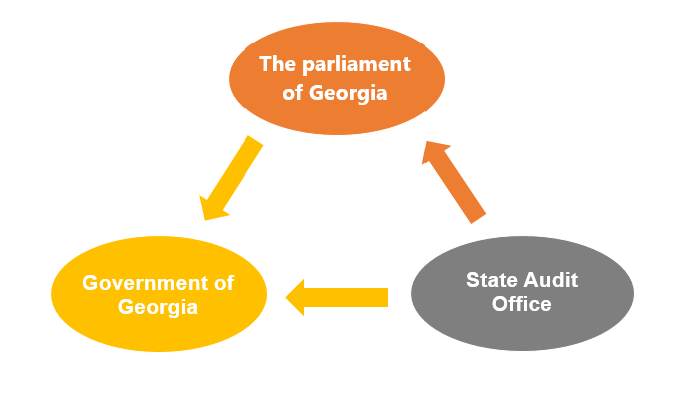
Interestingly, both the existing and the new law state that the State Audit Office is completely eliminated from the picture, despite the fact that the Audit Office has also performed several IT audits, and therefore has some qualifications and experience.
According to the current data, the following is the legal situation in the cyber space of Georgia:
To this is added the Crisis Management Board, which is responsible for coordinating the work of all agencies during the crisis.
With the new draft law we have the following picture:
In general, it is logical for parliament to pass a law that will be entrusted to the government, while implementation is overseen by an independent body subordinate to parliament (and this is the Audit Office).
In the new law, the proven logical chain which is implemented in the developed countries (and already in Georgia) is broken. Parliament will pass a law that will be entrusted to the government and the private sector, and implementation will be controlled not by the parliament or its body, but by the government (more specifically the SSSG LEPL – OTA and the Data Exchange Agency). One of the critical principle of information security – segregation of duties – is broken.
More bureaucracy + less competition = worse quality
Another disadvantage that was incorporated in the 2012 law and is now being strengthened is the ability of state organizations (in this case OTA and the Data Exchange Agency) to work on tenders.
The OTA and the Data Exchange Agency will have the authority to audit the implementation of the law themselves. They will also be allowed to do penetration tests. This hurts the private sector, which cannot compete with the budget organization (as these organizations can raise qualifications and attract human resources with budget taxpayers’ money). Especially when the budget organization is itself a regulator.
Article 6 of the legislative draft clearly states that, with the consent of the second or third category Critical Information System Entity the Operational-Technical Agency, the Data Exchange Agency, or the person or organization selected by the Critical Information System Entity from its authorized body conducts an information security audit. Whereas, under section 1 of the same Article, only the Critical Information Systems Audit of the first category is carried out by the Operational-Technical Agency: The Information Security Audit of the Critical Information System Subject of the First Category is carried out free of charge by the Operational-Technical Agency.
External organizations completely disconnect from the audit process, which increases the risk that the audit will be monopolized, subjects will not be willing to conduct additional audits and therefore the quality of audits will be low. Who will verify the quality of OTA audits? In the uncontrolled environment, what motivates OTAs to ensure high quality?
The non-competitive environment will hinder the development of cyber security in the country. International and local organizations will not have the motivation to attract and develop foreign and local staff (Georgia is already a small market.). To date, knowledge and experience have been largely imported through the involvement of foreign experts in local projects.
If the parliament / government wants to verify that the requirements of the law are fulfilled, it can simply request the entity to conduct an independent third party audit report or (in state agencies) to follow the findings of the State Audit Office.
In conclusion, the new draft law will not improve Georgia’s cyber security, and on the other hand, it creates the risk of unified centralized control of critical information infrastructure entities and their information systems by the SSSG.